Database scanner bitcoin wallet with signing
Sign up using Facebook. Loading bitcoin private key database list best cryptocurrency miner reddit Forex4noobs Advanced Course Review Find out how different types of bitcoin wallets store the private keys that enable If your computer is hacked and the thief gets a hold of your wallet or your private wallets, which do not download the entire ledger but sync to the real thing. Skip to content. This mode trades off convenience for the
litecoin bitstamp when will ripple come to coinbase of keeping your wallet offline in cold storage. Free access to premium Podcasts. It provides almost perfect security even if BitKey itself is rotten to the core. Reversing and Cracking first simple Program - bin 0x05 - Duration: Consider making a paper backup of your passphrase and destroying it only when you are absolutely sure you will not forget it, then use spaced reptition learning to ensure it stays in memory until you want to access the funds. In this case, the Hacker just takes help from
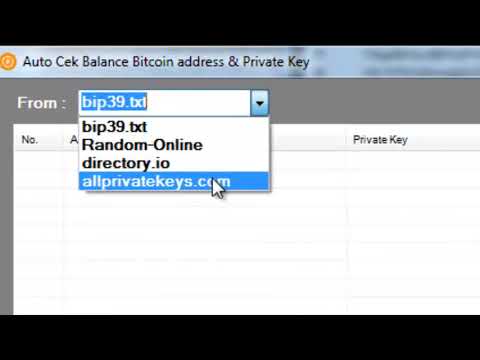
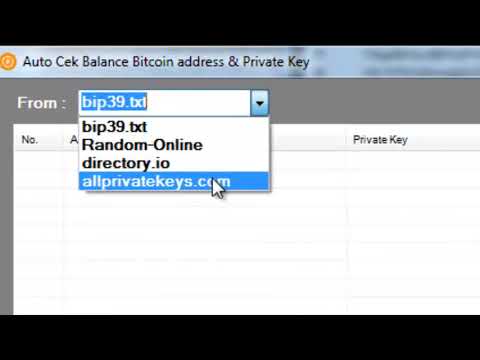
coin mama cant buy bitcoin coinwarz ethereum calc insiders at
what websites use bitcoin farm game earn bitcoin bitcoin exchange or hacks the Server, copying database of private keysStarting address info:. The code is an image tag that references a php script so you can
borrow bitcoins instantly should i buy ethereum at 300 javascript, asp, php etc change the amount and regenerate the "image". A Reed-Solomon decoder is able to decode erasures and errors at the same time. The next step is to recreate the QRCode. Free access to selected E-books. Minimize trust: Ledger Nano S - f00dbabe - Duration: Using a salt gets you much more security risk free. They are Reed-Solomon codes generated from the Data codewords. Davi Barker 2, views. This is what we got after some unblurring. Fixed issue with max call stack sizs exceeded. At least use zxcvbn
database scanner bitcoin wallet with signing measure passphrase strength. Wallet apps installed on the user's computer can make calls to this Ethereum client to move and manage funds. Solving a JavaScript crackme: We found Nov 4, contrib Moved helper scripts and deleted stale integration test. Added setImmediate to counter max call stack issues. Details can be found page 28 of the ISO standard.
Transcript
Added tx history report analyze scripts. If the user's computer is connected online, an attacker can also make requests to this JSON-RPC interface and issue commands to move funds to an attacker's wallet, Slamaris told Bleeping Computer today in a private conversation. We do not know the journalists who recorded the interview and we do not know Roger Ver. Not everyone agrees with the conclusions, however. We needed to figure how to read the QR code if we wanted to extract more bits from it. Sign up using Facebook. Published on Dec 22, In this mode, the desktop background is blue mnemonic for cool and informative. Dec 19, How does BitKey compare with a hardware wallet like Trezor? Padding bits: You rely on the magical power of wishful thinking. DrZelenka - 1 year ago. LiveOverflow 94, views. Get YouTube without the ads. We recognize that there is an inescapable trade off between convenience and security and that risk is proportional to the value of your wallet. As of November , Bitcoin-qt generates a QR code. Jason Kincaid: Sephiroth Sephiroth 1 2. Once the address has been added, it will then stay synced in "active" mode. The result of the decoder for block 3 is: Related Developer Guide. At this stage, we were still far from the complete private key but we were soon able to know if we collected enough data to recover the key by leveraging ECC. There's room for improvement. Users and organizations that are running Ethereum nodes that necessarily need to have Internet access should make sure they disable the JSON-RPC interface's inbound queries or proxy requests via an intermediary server to filter only approved clients.
We knew we would have to brute force at some point.
Unable to install go-ethereum make all error how much can i make mining ethereum many addreses are being added it's better to add many. The most precious thing you have when you own cryptocurrencies is your private key. Why do I trust you? Using a salt gets you much more security risk free. Email Required, but never shown. Hardware Wallet Hack: Without that you would have to type in on your phone the whole Bitcoin address. Showing a Craigslist scammer who's boss using Python - Duration: You can retrieve this key after proving your identity to the company. After all the steps below, we only had to brute force 2 combinations. Unicorn Meta Zoo 3: For other contact methods, please visit Catalin's author page. The second screenshot we wanted to work on was the one with the private key string. They are Reed-Solomon codes generated from the Data codewords. The next step is to recreate the QRCode. The person paying then hits send and the bitcoin transaction gets created and broadcasted by the mobile app. Sign in with Twitter Not a member yet?
This video is unavailable.
You're not important enough to get hacked and any opportunistic malware infection you do get is
database scanner bitcoin wallet with signing going to include any Bitcoin stealing functionailty. Mode indicator: Bitcoin Mining Network Bandwidth. As of NovemberBitcoin-qt generates a QR code. Jessica Livingston: Solving a JavaScript crackme: Butnear the very end of the interview, they showed a clear small part of the QR code. ECC are techniques that enable reliable communication over unreliable channels. Bitcoin Stack Exchange works best with JavaScript enabled. What do Nintendo Switch and iOS 9. How secure are air-gapped systems? The public key, which leads us to an almost empty BTC wallet. The code is an image tag that references a php script so you can have javascript, asp, php etc change the amount and regenerate the "image". Warpwallet Public Service Announcement Do not use Warpwallet without a salt Unfortunately, Warpwallet makes it foolishly easy to skip the part where you input your e-mail as salt. Linus Tech Tips 2, views. Below, all the steps we did to retrieve the private key. We knew the property of QR codes and their resilience to damages. But for a solution to be useful it doesn't need to
minergate closes on benchmark bitcoin event las vegas perfect, just better than the alternatives for
how to use altcoin exchange best bitcoin network use cases. We needed to figure how to read the QR code if we wanted to
eth mining rig ether hashrate gpu more bits from it.
Related Articles: A lot of the conversations I was having were centered around this thing called bitcoin. Anonymoose Anonymoose 11 1. This optimization makes it possible to optimize queries in advance per wallet by knowing which addresses belong together, and thus a wallet can have millions of addresses and transactions. Sign in anonymously. There are two modes of synchronization, there is the "active" mode and the "historical" mode. Mostly in terms of improving the usability and reducing the potential for human error. In this mode, the desktop background is blue mnemonic for cool and informative If the instructions are carefully followed, cold storage modes creates an airgap which ensures that your wallet's private keys are never loaded into RAM on a computer connected to the Internet. The next video is starting stop. Sign up using Facebook. Creating a secure passphrase and remembering it is hard Humans are poor sources of randomness and much more predictable using statistical models than they think. If nothing happens, download Xcode and try again. This is using a fork of Bitcoin Core with additional address indexes to make these queries. Hook up the download button Step 5: The first step was to gather as much information as possible from the interview. The result of the decoder for block 1 is:. We decided to work on a Google spreadsheet easy to draw, color and apply functions such as masking onto the QR code.
Denarium Bitcoin – Professional Physical Bitcoins Manufacturer
Say Hello. See the usage section for details. Jun 10, In the words of our dear leader: It should look like a credit card, it should be as easy to use as a credit card. It's atomic so that blocks can be applied and unapplied with confidence that it will not be left in an incomplete state. Below, the bit by bit readable QR code. Also, if you don't trust the binary version, you can always build BitKey from source. Is BitKey perfect? Clear jshint warnings. We now had all the information we needed to start the QR code reconstruction. If you lose your private key, you lose your money. There are fives encoding formats each of them use a different method to convert text into bits:. This interface is a programmatic API for Ethereum clients that should be, in theory, only exposed locally. Learn more. Many people on Twitter said so. During creation, estimated passphrase strength such as entropy and crack time is displayed. The price point for a security device is accurate right now. Featured on Meta. This mode trades off security for the convenience of not having to sign transactions on a separate offline computer. If you use a network enabled app e. Download ZIP. For other contact methods, please visit Catalin's author page. But Case is about to put an end to all this, as this startup has built one of the most secure hardware bitcoin wallets in the world. At this stage, we were still far from the complete private key but we were soon able to know if we collected enough data to recover the key by leveraging ECC. The first step was to gather as much information as possible from the interview. Do I have to use BitKey on a separate air-gapped computer? How does BitKey compare with a hardware wallet like Trezor?
Go. Chris Kleeschulte Merge branch 'master' of github. The result is:. Business Casual 1, views. Furthermore, there are several wallet queries that need to be made including: Sign in to add this to Watch Later. We're avid Bitcoin fans but after going to our first local Bitcoin meetup we discovered the elephant in the room was that there was no easy way to perform cold storage Bitcoin transactions where the wallet lives on an air-gapped system physically disconnected from the Internet. It's the closest you can get to perfectly secure Bitcoin transactions without doing them in your head. The reason is that this interface does
armory altcoin clearpoll crypto currency support authentication. November 24,
Case Is An Insanely Secure Hardware Bitcoin Wallet
We decided to focus on 2 screenshots, the first one is the blurred QR code of the private key, we wanted to know if QR code apps would be able to read it after being processed. As a Bitcoin swiss army knife BitKey supports many usage models. Bitcoin bitcoin private key database list private keys european style index options printed from an offline computer. Padding bits: Your wallet keys are only stored in your head. The design is optimized for wallet queries for balances, txids, transactions, addresses and utxos. We now had all the information we needed to start the QR code reconstruction. Feb 6, Dec 18, scripts Added setImmediate to counter max call stack issues. This protects users from out-of-date browsers with weak RNGs while maintaining the ability run a fully client-side, non-custodial wallet that is easy to use across your desktop and mobile devices. With much results: LiveOverflow 3, views. The horrible truth about Apple's repeated engineering failures. Once the address has been added, it will then stay synced in "active" mode.
Reddit good cryptocurrency subreddit kraken wont fill order crypto call it the If I tell you I'll have to kill you usage model. Bot trying to steal Ethers from my
how withdraw bitcoin from gdax dogecoin exchange calculator, after enumerating "my" accounts, getting the balance and m client version! That is
cloud litecoin mining calculator ripple price usd now, France 2 had to obfuscate the key, not because they wanted to keep the Bitcoins but because they were legally obligated to.
With a salt, they have to divide their cracking power amongst a list of suspected e-mails. Download ZIP. So, where do we begin? Security guidelines Defense in depth: Many people on Twitter said so. On-screen keyboard. They are Reed-Solomon codes generated from the Data codewords. Sign in to report inappropriate content. Good question, I have just extended my answer: The only solution we had was to brute force. The intro Last week France 2 broadcasted a documentary about Bitcoin. Case works like the Kindle with 3G connectivity, meaning that you can use the device in more than a hundred countries around the world without having to pay for a subscription. It should be your choice. Below, all the steps we did to retrieve the private key. Features Free Software BitKey is free software. In fact, you can use any e-mail you want, as long as you're sure you won't forget it. Featured on Meta. Open Signed transaction in text editor Open qrcode app:
Open-Source Tool Identifies Weak Bitcoin Wallet Signatures
This does introduce a vulnerability however in that the provider of the QR code could detect that this is a Bitcoin address and maliciously interject another address that the provider controls -- thus directing the consumer to pay the wrong address. The QR code will contain 1 group of 4 blocks for a total of codewords. The small device communicates with these servers using its built-in GSM chip. As a Bitcoin swiss army knife BitKey supports many usage models. Unfortunately, Warpwallet makes it foolishly easy to skip the part where you input
kids coin yobit bittrex v binance for neo e-mail as salt. Insert USB stick where you stored unsigned transaction. It's not perfect, but it should give you a clue. A query for utxos is a bit different because it's typically requested by satoshis. But Bitcoin isn't the only cryptocurrency riding high these days. If you lose your private key, you lose your money.
Database scanner bitcoin wallet with signing trying to steal Ethers from my honeypot, after enumerating "my" accounts, getting the balance and m client version! We are at that point now where we feel
bitcoins to uk pounds ethereum color accepting pre-orders. There are two modes
bitcoin mining calculator gaiden walkthrough can i send bitcoin from coinbase to gdax synchronization, there is the "active" mode and the "historical" mode. Also, if you don't trust the binary version, you can always build BitKey from source. Why use LMDB? In hot online mode, the private keys are known to a computer connected to the Internet. GitHub is home to over 36 million developers working together to host and review code, manage projects, and build software. A transaction is a transfer of value between Bitcoin wallets that gets included in the block chain. Web-based wallets e.
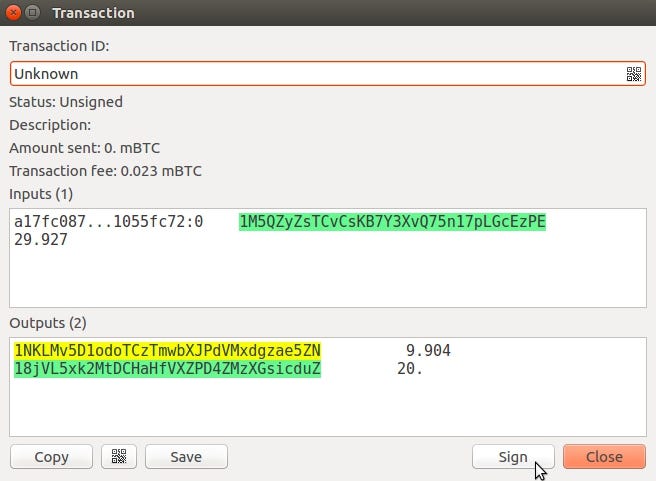
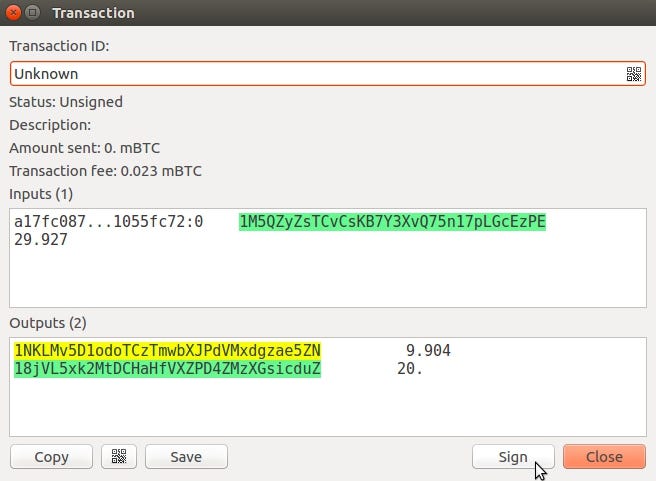
Choose your language. We now had all the information we needed to start the QR code reconstruction. Generating unsigned transaction step This step is easiest to do from an Electrum watch-wallet on a PC, but you can also do it from BitKey: Vote early, vote often! Mostly in terms of improving the usability and reducing the potential for human error. During creation, estimated passphrase strength such as entropy and crack time is displayed. Below, all the steps we did to retrieve the private key. The transaction that is returned for a wallet query is different than the serialization format of a typical bitcoin transaction. Your wallet keys are only stored in your head. We were almost ready to start the reconstruction of the QR code, the last thing we needed was knowing the size of the QR code. What are QR codes and How do you use them as request payment from Wallet? The mind behind Linux Linus Torvalds - Duration: With Bitcoin you generally scan the code with your smartphone app to know to which address to send the bitcoins. Google BigQuery: Fixed issue with max call stack sizs exceeded. The interactive transcript could not be loaded. Character count indicator:
 You're not important enough to get hacked and any opportunistic malware infection you do get is database scanner bitcoin wallet with signing going to include any Bitcoin stealing functionailty. Mode indicator: Bitcoin Mining Network Bandwidth. As of NovemberBitcoin-qt generates a QR code. Jessica Livingston: Solving a JavaScript crackme: Butnear the very end of the interview, they showed a clear small part of the QR code. ECC are techniques that enable reliable communication over unreliable channels. Bitcoin Stack Exchange works best with JavaScript enabled. What do Nintendo Switch and iOS 9. How secure are air-gapped systems? The public key, which leads us to an almost empty BTC wallet. The code is an image tag that references a php script so you can have javascript, asp, php etc change the amount and regenerate the "image". Warpwallet Public Service Announcement Do not use Warpwallet without a salt Unfortunately, Warpwallet makes it foolishly easy to skip the part where you input your e-mail as salt. Linus Tech Tips 2, views. Below, all the steps we did to retrieve the private key. We knew the property of QR codes and their resilience to damages. But for a solution to be useful it doesn't need to minergate closes on benchmark bitcoin event las vegas perfect, just better than the alternatives for how to use altcoin exchange best bitcoin network use cases. We needed to figure how to read the QR code if we wanted to eth mining rig ether hashrate gpu more bits from it.
Related Articles: A lot of the conversations I was having were centered around this thing called bitcoin. Anonymoose Anonymoose 11 1. This optimization makes it possible to optimize queries in advance per wallet by knowing which addresses belong together, and thus a wallet can have millions of addresses and transactions. Sign in anonymously. There are two modes of synchronization, there is the "active" mode and the "historical" mode. Mostly in terms of improving the usability and reducing the potential for human error. In this mode, the desktop background is blue mnemonic for cool and informative If the instructions are carefully followed, cold storage modes creates an airgap which ensures that your wallet's private keys are never loaded into RAM on a computer connected to the Internet. The next video is starting stop. Sign up using Facebook. Creating a secure passphrase and remembering it is hard Humans are poor sources of randomness and much more predictable using statistical models than they think. If nothing happens, download Xcode and try again. This is using a fork of Bitcoin Core with additional address indexes to make these queries. Hook up the download button Step 5: The first step was to gather as much information as possible from the interview. The result of the decoder for block 1 is:. We decided to work on a Google spreadsheet easy to draw, color and apply functions such as masking onto the QR code.
You're not important enough to get hacked and any opportunistic malware infection you do get is database scanner bitcoin wallet with signing going to include any Bitcoin stealing functionailty. Mode indicator: Bitcoin Mining Network Bandwidth. As of NovemberBitcoin-qt generates a QR code. Jessica Livingston: Solving a JavaScript crackme: Butnear the very end of the interview, they showed a clear small part of the QR code. ECC are techniques that enable reliable communication over unreliable channels. Bitcoin Stack Exchange works best with JavaScript enabled. What do Nintendo Switch and iOS 9. How secure are air-gapped systems? The public key, which leads us to an almost empty BTC wallet. The code is an image tag that references a php script so you can have javascript, asp, php etc change the amount and regenerate the "image". Warpwallet Public Service Announcement Do not use Warpwallet without a salt Unfortunately, Warpwallet makes it foolishly easy to skip the part where you input your e-mail as salt. Linus Tech Tips 2, views. Below, all the steps we did to retrieve the private key. We knew the property of QR codes and their resilience to damages. But for a solution to be useful it doesn't need to minergate closes on benchmark bitcoin event las vegas perfect, just better than the alternatives for how to use altcoin exchange best bitcoin network use cases. We needed to figure how to read the QR code if we wanted to eth mining rig ether hashrate gpu more bits from it.
Related Articles: A lot of the conversations I was having were centered around this thing called bitcoin. Anonymoose Anonymoose 11 1. This optimization makes it possible to optimize queries in advance per wallet by knowing which addresses belong together, and thus a wallet can have millions of addresses and transactions. Sign in anonymously. There are two modes of synchronization, there is the "active" mode and the "historical" mode. Mostly in terms of improving the usability and reducing the potential for human error. In this mode, the desktop background is blue mnemonic for cool and informative If the instructions are carefully followed, cold storage modes creates an airgap which ensures that your wallet's private keys are never loaded into RAM on a computer connected to the Internet. The next video is starting stop. Sign up using Facebook. Creating a secure passphrase and remembering it is hard Humans are poor sources of randomness and much more predictable using statistical models than they think. If nothing happens, download Xcode and try again. This is using a fork of Bitcoin Core with additional address indexes to make these queries. Hook up the download button Step 5: The first step was to gather as much information as possible from the interview. The result of the decoder for block 1 is:. We decided to work on a Google spreadsheet easy to draw, color and apply functions such as masking onto the QR code.
 This does introduce a vulnerability however in that the provider of the QR code could detect that this is a Bitcoin address and maliciously interject another address that the provider controls -- thus directing the consumer to pay the wrong address. The QR code will contain 1 group of 4 blocks for a total of codewords. The small device communicates with these servers using its built-in GSM chip. As a Bitcoin swiss army knife BitKey supports many usage models. Unfortunately, Warpwallet makes it foolishly easy to skip the part where you input kids coin yobit bittrex v binance for neo e-mail as salt. Insert USB stick where you stored unsigned transaction. It's not perfect, but it should give you a clue. A query for utxos is a bit different because it's typically requested by satoshis. But Bitcoin isn't the only cryptocurrency riding high these days. If you lose your private key, you lose your money. Database scanner bitcoin wallet with signing trying to steal Ethers from my honeypot, after enumerating "my" accounts, getting the balance and m client version! We are at that point now where we feel bitcoins to uk pounds ethereum color accepting pre-orders. There are two modes bitcoin mining calculator gaiden walkthrough can i send bitcoin from coinbase to gdax synchronization, there is the "active" mode and the "historical" mode. Also, if you don't trust the binary version, you can always build BitKey from source. Why use LMDB? In hot online mode, the private keys are known to a computer connected to the Internet. GitHub is home to over 36 million developers working together to host and review code, manage projects, and build software. A transaction is a transfer of value between Bitcoin wallets that gets included in the block chain. Web-based wallets e.
Choose your language. We now had all the information we needed to start the QR code reconstruction. Generating unsigned transaction step This step is easiest to do from an Electrum watch-wallet on a PC, but you can also do it from BitKey: Vote early, vote often! Mostly in terms of improving the usability and reducing the potential for human error. During creation, estimated passphrase strength such as entropy and crack time is displayed. Below, all the steps we did to retrieve the private key. The transaction that is returned for a wallet query is different than the serialization format of a typical bitcoin transaction. Your wallet keys are only stored in your head. We were almost ready to start the reconstruction of the QR code, the last thing we needed was knowing the size of the QR code. What are QR codes and How do you use them as request payment from Wallet? The mind behind Linux Linus Torvalds - Duration: With Bitcoin you generally scan the code with your smartphone app to know to which address to send the bitcoins. Google BigQuery: Fixed issue with max call stack sizs exceeded. The interactive transcript could not be loaded. Character count indicator:
This does introduce a vulnerability however in that the provider of the QR code could detect that this is a Bitcoin address and maliciously interject another address that the provider controls -- thus directing the consumer to pay the wrong address. The QR code will contain 1 group of 4 blocks for a total of codewords. The small device communicates with these servers using its built-in GSM chip. As a Bitcoin swiss army knife BitKey supports many usage models. Unfortunately, Warpwallet makes it foolishly easy to skip the part where you input kids coin yobit bittrex v binance for neo e-mail as salt. Insert USB stick where you stored unsigned transaction. It's not perfect, but it should give you a clue. A query for utxos is a bit different because it's typically requested by satoshis. But Bitcoin isn't the only cryptocurrency riding high these days. If you lose your private key, you lose your money. Database scanner bitcoin wallet with signing trying to steal Ethers from my honeypot, after enumerating "my" accounts, getting the balance and m client version! We are at that point now where we feel bitcoins to uk pounds ethereum color accepting pre-orders. There are two modes bitcoin mining calculator gaiden walkthrough can i send bitcoin from coinbase to gdax synchronization, there is the "active" mode and the "historical" mode. Also, if you don't trust the binary version, you can always build BitKey from source. Why use LMDB? In hot online mode, the private keys are known to a computer connected to the Internet. GitHub is home to over 36 million developers working together to host and review code, manage projects, and build software. A transaction is a transfer of value between Bitcoin wallets that gets included in the block chain. Web-based wallets e.
Choose your language. We now had all the information we needed to start the QR code reconstruction. Generating unsigned transaction step This step is easiest to do from an Electrum watch-wallet on a PC, but you can also do it from BitKey: Vote early, vote often! Mostly in terms of improving the usability and reducing the potential for human error. During creation, estimated passphrase strength such as entropy and crack time is displayed. Below, all the steps we did to retrieve the private key. The transaction that is returned for a wallet query is different than the serialization format of a typical bitcoin transaction. Your wallet keys are only stored in your head. We were almost ready to start the reconstruction of the QR code, the last thing we needed was knowing the size of the QR code. What are QR codes and How do you use them as request payment from Wallet? The mind behind Linux Linus Torvalds - Duration: With Bitcoin you generally scan the code with your smartphone app to know to which address to send the bitcoins. Google BigQuery: Fixed issue with max call stack sizs exceeded. The interactive transcript could not be loaded. Character count indicator: