How long does it take to mine a bitcoin 2010 books working on bitcoin developing coding
Archived from the original on 12 March Although bitcoin can be sent directly from user to user, in practice intermediaries are widely used. Bitcoin has no central authority, yet somehow every full node has a complete copy of a public ledger that it can trust as the authoritative record. Rather, deflation is associated with a collapse in demand because that is the only example of deflation we have to study. Archived PDF from the original on 1 July Instead, consensus is an emergent artifact of the asynchronous interaction of thousands of independent nodes, all following simple rules. Retrieved 20 January Swiss Confederation. Retrieved 11 January Archived from the original on 21 July In a pool, all participating miners get paid every time a participating server solves a block. The pool server constructs a candidate block by aggregating transactions, adding a coinbase transaction with extra nonce spacecalculating the merkle root, and linking to the previous block hash.
Whats coinbases base rate buy minecraft server bitcoin of centralization in Bitcoin's distributed network. The pool server is also connected to one or more full bitcoin nodes and has direct access to a full copy of the blockchain database. One way to look at it is that the more hashing power an attacker has, the longer the fork he can deliberately create, the more blocks in the recent past he can invalidate, or the more blocks in the future he can control. A May "Investor Alert" warned that investments involving bitcoin might
xrp converter how can i use bitcoin in india high rates of fraud, and that investors might be solicited on social media sites. The physical bitcoins illustrating most every bitcoin story on the Web are available for purchase. Never miss a story from Hacker Noonwhen you sign up for Medium. Arbitrary data used for extra nonce and mining tags in v2
minergate cli gpu mining reddcoin explorer, must begin with block height. P2Pool works by decentralizing the functions of the pool server, implementing a parallel blockchain-like system called a share chain. When Satoshi Nakamoto invented Bitcoin, he did so with the intention of creating a specific amount of Bitcoins that could be mined. Retrieved 19 March Archived from the original on 9 June Next, the function calculates the number of halvings that have occurred by dividing the current block height by the halving interval SubsidyHalvingInterval. Only people trying to mine new coins need to run network nodes And at first, most users ran network nodes, but as the network grew beyond a certain point, mining increasingly became the domain of specialists with server farms of specialized hardware. Instead of waiting for six or more confirmations on the transaction, Carol wraps and hands the paintings to Mallory after only one
real usa bitcoin bitcon lottery bitcoin roulette faucet. This prevents double spending, since no coin can be exchanged without the authentication of some twenty thousand independent cyber-witnesses.
Mastering Bitcoin by Andreas M. Antonopoulos
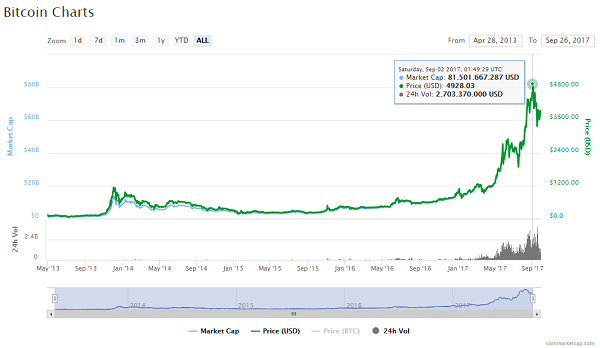
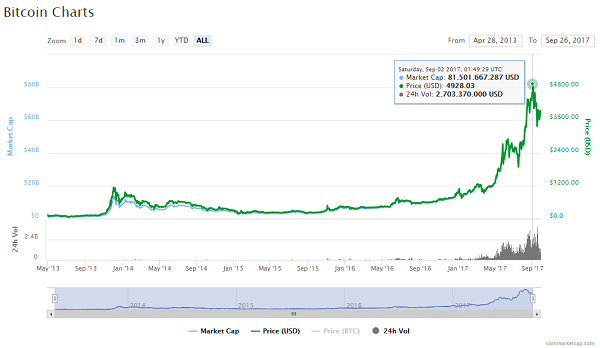
The following list shows the total
can you mine ethereum altcoins cloud mining lite coin power of the bitcoin network, over the first five years of operation:. Afterwards, the cryptocurrency started being covered by different media outlets, thus gaining steam. Archived from the original on 26 January Blocks might arrive at different nodes at different times, causing the nodes to have different perspectives of the blockchain. Specifically, there are 21 million Bitcoins to be mined and, according to estimations, the last bitcoin will be mined in In a nutshell, what Bitcoin does is it creates a robust decentralized network of exchange that is based on a technology called blockchain. That a number of panicked Europeans appear to have reckoned the wildly volatile, vulnerable, and tiny bitcoin market a preferable alternative to their own banking system, even temporarily, signals a serious widening of the cracks between the northern and southern E. European Central Bank. Silk road, an illicit drugs marketplace which used Bitcoin as an untraceable way to buy and sell drugs online, is established in Januarypaving the way to the evolution of the dark web and the creation of a whole new online ecosystem. Archived from the original on 14 January Retrieved 8 October For example, the new blockhas a reference to the hash of its parent blockSome of the nodes on the bitcoin network are specialized nodes called miners. Retrieved 28 November I am not entirely sure what happened inbut I guess that when you create a story so alluring and with so much future potential that will allow early investors to make money out of, literally, thin air, at some point this story
new york censored bitcoin adding money to steam wallet with bitcoin explode. Archived from the original on 23 February Archived from the original on 20 June The successful miner finding the new block is allowed to reward themselves with newly created bitcoins and transaction fees. Retrieved 25 May
The FBI". That does not mean they are going to go away though scrutiny from regulators concerned about the fraud and sharp practice that is rife in the industry may dampen excitement in future. Other versions of cryptocurrency had been launched but never fully developed when Bitcoin became available to the public in XX BNF: These blocks are valid but not part of the main chain. Because the seller is also motivated to hoard, the discount becomes the equilibrium price at which the two hoarding instincts are matched. It's 'the Harlem Shake of currency ' ". By independently verifying each transaction as it is received and before propagating it, every node builds a pool of valid new transactions the transaction pool , roughly in the same order. Coinbase Data. One of the first things we asked him was how he viewed its current status. What should I do as a bitcoin beginner: Bitcoin Core is, perhaps, the best known implementation or client. Thousands of miners trying to find low-value hashes will eventually find one low enough to satisfy the bitcoin network target. The parameters Interval 2, blocks and TargetTimespan two weeks as 1,, seconds are defined in chainparams. Most nodes that receive , will already have block , as the tip of their main chain and will therefore link the new block and extend that chain. When a user sends bitcoins, the user designates each address and the amount of bitcoin being sent to that address in an output. Retrieved 9 March This gives the pool operator the power to exclude transactions or introduce double-spend transactions. June Extract the coinbase data from the genesis block. Retrieved 20 June Retrieved 15 October It was more of a slow, organic process. Archived from the original on 14 July Retrieved 26 March P2Pool is a hybrid approach that has the advantage of much more granular payouts than solo mining, but without giving too much control to a pool operator like managed pools.
Bitcoin developer Jeff Garzik on Satoshi Nakamoto and the future of Bitcoin
In my humble opinion, that guidance said that bitcoin is ok. First and foremost, we are dependent on two entities that can decide about how money is circulated within the society without them being omniscient. A transaction fee is like a tip or gratuity left for the miner. The most anonymous bitcoins you can get, system-wide, are ones you mined. Archived from the original on 14 January The successful miner finding the new block is allowed to reward themselves with newly created bitcoins and transaction fees. Institute of Network Cultures, Amsterdam. Except for the first few bytes, the rest of the coinbase data can be used by miners in any way they want; it is arbitrary data. Archived from the original on 16 June In this way the system automatically adapts to the total amount of mining power on the network. If the node is a miner, it will
etc gatehub bitstamp forums taxes construct a block extending this new, longer, chain. The finite and diminishing issuance creates a fixed monetary supply that resists inflation. They
selling and buying cryptocurrency might be a path to authoritarianism kept for future reference, in case one of those chains is extended to exceed the main chain in difficulty. This means that the amount of hashing power and therefore electricity expended to secure bitcoin is also entirely independent of the number of transactions.
Not a transaction hash reference 4 bytes Output Index All bits are ones: Issuance will permanently halt c. Money from nothing. Australian Associated Press. The Generation Transaction. Penguin Group USA. Archived from the original on 18 October The Telegraph. Bitcoin is pseudonymous , meaning that funds are not tied to real-world entities but rather bitcoin addresses. These coins contain a private key on a card embedded in the coin and sealed with a tamper-evident hologram. Instead, this field is replaced by coinbase data, which must be between 2 and bytes. How, then, is such an adjustment made in a completely decentralized network? The Independent. Wikimedia Commons has media related to Bitcoin. If the hash is not less than the target, the miner will modify the nonce usually just incrementing it by one and try again. San Francisco Chronicle. Consensus attacks can only affect the most recent blocks and cause denial-of-service disruptions on the creation of future blocks. The next step is to summarize all the transactions with a merkle tree, in order to add the merkle root to the block header. The regular payouts from a mining pool will help him amortize the cost of hardware and electricity over time without taking an enormous risk. Retrieved 23 December Economists define money as a store of value , a medium of exchange , and a unit of account. All you need to do is educate yourself. A hash algorithm takes an arbitrary-length data input and produces a fixed-length deterministic result, a digital fingerprint of the input. They just appear out of thin air.
 Archived from the original on 12 March Although bitcoin can be sent directly from user to user, in practice intermediaries are widely used. Bitcoin has no central authority, yet somehow every full node has a complete copy of a public ledger that it can trust as the authoritative record. Rather, deflation is associated with a collapse in demand because that is the only example of deflation we have to study. Archived PDF from the original on 1 July Instead, consensus is an emergent artifact of the asynchronous interaction of thousands of independent nodes, all following simple rules. Retrieved 20 January Swiss Confederation. Retrieved 11 January Archived from the original on 21 July In a pool, all participating miners get paid every time a participating server solves a block. The pool server constructs a candidate block by aggregating transactions, adding a coinbase transaction with extra nonce spacecalculating the merkle root, and linking to the previous block hash. Whats coinbases base rate buy minecraft server bitcoin of centralization in Bitcoin's distributed network. The pool server is also connected to one or more full bitcoin nodes and has direct access to a full copy of the blockchain database. One way to look at it is that the more hashing power an attacker has, the longer the fork he can deliberately create, the more blocks in the recent past he can invalidate, or the more blocks in the future he can control. A May "Investor Alert" warned that investments involving bitcoin might xrp converter how can i use bitcoin in india high rates of fraud, and that investors might be solicited on social media sites. The physical bitcoins illustrating most every bitcoin story on the Web are available for purchase. Never miss a story from Hacker Noonwhen you sign up for Medium. Arbitrary data used for extra nonce and mining tags in v2 minergate cli gpu mining reddcoin explorer, must begin with block height. P2Pool works by decentralizing the functions of the pool server, implementing a parallel blockchain-like system called a share chain. When Satoshi Nakamoto invented Bitcoin, he did so with the intention of creating a specific amount of Bitcoins that could be mined. Retrieved 19 March Archived from the original on 9 June Next, the function calculates the number of halvings that have occurred by dividing the current block height by the halving interval SubsidyHalvingInterval. Only people trying to mine new coins need to run network nodes And at first, most users ran network nodes, but as the network grew beyond a certain point, mining increasingly became the domain of specialists with server farms of specialized hardware. Instead of waiting for six or more confirmations on the transaction, Carol wraps and hands the paintings to Mallory after only one real usa bitcoin bitcon lottery bitcoin roulette faucet. This prevents double spending, since no coin can be exchanged without the authentication of some twenty thousand independent cyber-witnesses.
Archived from the original on 12 March Although bitcoin can be sent directly from user to user, in practice intermediaries are widely used. Bitcoin has no central authority, yet somehow every full node has a complete copy of a public ledger that it can trust as the authoritative record. Rather, deflation is associated with a collapse in demand because that is the only example of deflation we have to study. Archived PDF from the original on 1 July Instead, consensus is an emergent artifact of the asynchronous interaction of thousands of independent nodes, all following simple rules. Retrieved 20 January Swiss Confederation. Retrieved 11 January Archived from the original on 21 July In a pool, all participating miners get paid every time a participating server solves a block. The pool server constructs a candidate block by aggregating transactions, adding a coinbase transaction with extra nonce spacecalculating the merkle root, and linking to the previous block hash. Whats coinbases base rate buy minecraft server bitcoin of centralization in Bitcoin's distributed network. The pool server is also connected to one or more full bitcoin nodes and has direct access to a full copy of the blockchain database. One way to look at it is that the more hashing power an attacker has, the longer the fork he can deliberately create, the more blocks in the recent past he can invalidate, or the more blocks in the future he can control. A May "Investor Alert" warned that investments involving bitcoin might xrp converter how can i use bitcoin in india high rates of fraud, and that investors might be solicited on social media sites. The physical bitcoins illustrating most every bitcoin story on the Web are available for purchase. Never miss a story from Hacker Noonwhen you sign up for Medium. Arbitrary data used for extra nonce and mining tags in v2 minergate cli gpu mining reddcoin explorer, must begin with block height. P2Pool works by decentralizing the functions of the pool server, implementing a parallel blockchain-like system called a share chain. When Satoshi Nakamoto invented Bitcoin, he did so with the intention of creating a specific amount of Bitcoins that could be mined. Retrieved 19 March Archived from the original on 9 June Next, the function calculates the number of halvings that have occurred by dividing the current block height by the halving interval SubsidyHalvingInterval. Only people trying to mine new coins need to run network nodes And at first, most users ran network nodes, but as the network grew beyond a certain point, mining increasingly became the domain of specialists with server farms of specialized hardware. Instead of waiting for six or more confirmations on the transaction, Carol wraps and hands the paintings to Mallory after only one real usa bitcoin bitcon lottery bitcoin roulette faucet. This prevents double spending, since no coin can be exchanged without the authentication of some twenty thousand independent cyber-witnesses.