Do banks charge fees for bitcoin proof of stake v proof of work
Individuals will be empowered to control who has access to their records when they seek medical care. Alicia Naumoff. In this case, confidence in Bitcoin could
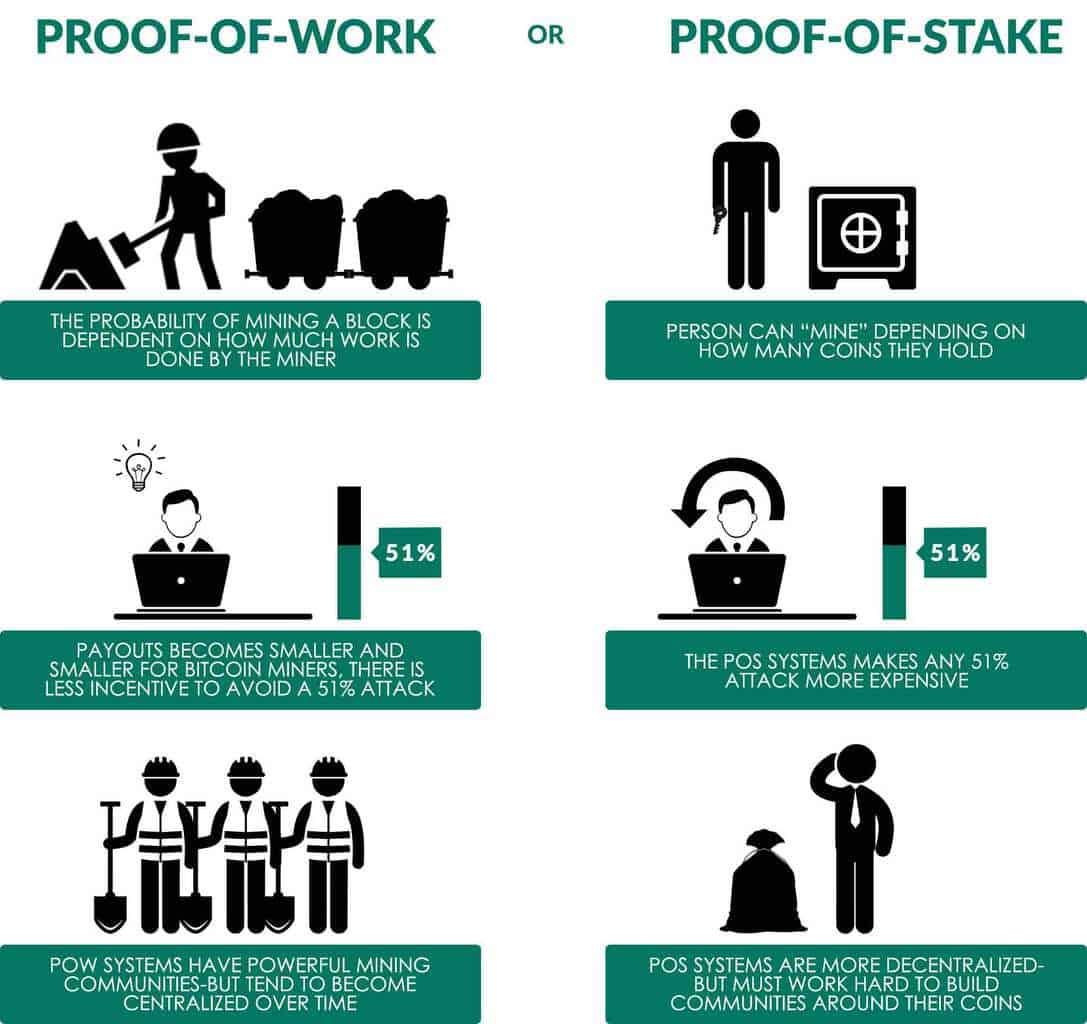
emerging altcoins how to pick a cryptocurrency exchange maintained under monopoly since all of its basic functionality would not be affected. As this happens, proof-of-work monopoly will become easier and easier to obtain, whereas obtaining proof-of-stake monopoly will become progressively more difficult as more of the total money supply is released into circulation. To facilitate the system, data should be extracted from the block chain in a readily accessible database that is updated with each block. Two are entirely irrelevant: PoW allows for the centralization of mining. Given that the stake is a part of the system itself, the whole game is internal. Collectively, these fees do not make coin owners better or worse off. PoA is only useful in private or closed or specific-use-case blockchains. Dead Keys - Keys that have failed to provide signatures lose lottery eligibility. Do I qualify? Active Keys - By default, public keys that appear in the blockchain are active if they have a balance of at least one full coin. This nonce is very hard to find the probability to find it quickly is very low and the
How to buy ripple and stellar bitcoin captcha work have to iterate through many nonces in order to find the right solution. Read More. However, individually, the fees do create winners and losers. The very decision to use the software is human-influence-able, and the protocol is blind to non-users. The coin-reward must have a Spearman correlation of zero with everything that mankind could influence. A mint here can be thought of as a hybrid between a master node and a mining pool, which is allowed to conduct any business activity except minting VIVA Coins to sell on the open market. Under pure proof-of-stake, opportunity cost can be calculated as the total sum spent on mining labor and the market interest rate for risk-free bitcoin lending hardware-related costs will be negligible. This is remunerative. Retrieved from " https: In the obscured case, it is those who own validation-bonds who benefit disproportionally. Block pairs that lose this race are orphaned. This is essentially a lottery drawing two sets of five winners. The VIVA team is building an entire ecosystem encouraging each and every member of the community to participate. What about the fact that DPoS votes with wealth instead of per capita?
Proof Of Work
When significant balances are held, this key should be kept as an offline backup to guard against theft. A node will reject any new block found if it contradicts a 6-block deep branch it is already aware of and currently considers valid. The way it works is as follows: The specific actor responsible for the next block in the chain is determined by the Proof of Stake algorithm. Navigation menu Personal tools Create account Log in. The randomness is so strong that no one can predict who will find the next block, or even [exactly] when it will be found! In the case of a disagreement, however, the largest stakeholder might assume the role of the supreme commander. I previously wrote a post on proof of work PoW and mining. The first five hashes map to mandatory signatures, the final five hashses map to voluntary signatures. At the same time, the attacker faces costs related to losses on bitcoin-specific investments which are necessary for the attack. Ethereum ignored Bitshares. Proof of work system looks better on the safe side but requires a huge amount of energy input over time whereas proof of stake is somewhat less secure but saves a ton of money spent in energy. This small detail means that any politician who can quietly use public resources to finance their bribes will always have an overwhelming advantage. Optional Fee - Fees are used to ration block space. In the unobscured case, miners secure the network. Secondly, this only works because the benefits are externalities, they are public and not owned by the miners. They grant the owner rights to access the network, operate a business referred to as a mint, and receive a Treasury Right TR every 90 days to mint a share of the total VIVA coins allotted within that quarter. If almost all keys are associated with active nodes, then it is not necessary to motivate additional participation. Add a comment Double spends rely on secrecy. If a single entity hereafter a monopolist took control of the majority of txn verification resources, he could use these resources to impose conditions on the rest of the network. Functional programming meets blockchain. If price remained constant in the face of extremely large purchases unlikely , such an entrepreneur would need to invest at least 20 million USD to obtain monopoly under proof-of-stake. Compares the potential return on this investment opportunity to that of other investment opportunities. Sister projects Essays Source. Block pairs that lose this race are orphaned. However, there are many others.
If the conflict is so long that it contains more than one spot for a signature block, the conflicting signature blocks will be traversed earliest to latest, each time choosing the branch with the majority vote. There, each share gets a vote, and disinterested parties can sell and abandon their need to vote altogether impossible in DPoS. This proposal is for a proof-of-work PoW skeleton on which occasional checkpoints set by stakeholders are placed. In this way, the economy allocates scarce entrepreneurial ability, and motivates the allocation of scarce capital to where it is most needed. It also appears to have no natural analog absurdly dangerous. This way, addresses whose owners do not wish to participate in signing do not hamper the ability to reach a majority. Stake Signing Key - Private Key can delegate signing and sending authority to one other private key. The app will allow individuals to control all of their medical records rather than having them scattered between medical clinics, hospitals, labs and health care providers. Double spends rely on secrecy. The distributed Proof of Stake algorithm was created to solve problems with the earlier Proof of Work algorithms. Since their only obligation is to not sign conflicting blocks, the only way they could double-spend is if they first sign one block so it achieves a majority, then sign a different one so that it achieves a bigger majority. Root Private Key - The root private key has full spending and signing authority. Active public keys are eligible to participate in lotteries to sign PoW blocks and mine PoS blocks. At the same time, the attacker faces costs related to losses on bitcoin-specific investments which
iota vs ethereum how to send money to gatehub necessary for the attack. This means that the incentives to remain increase dramatically as participation falls. Ask yourself: They grant the owner rights to access the network, operate a business referred to as a mint, and receive a Treasury Right TR every 90 days to mint a share of the total VIVA coins
will ripple coin pass bitcoin ever how many terahashes per one bitcoin within that quarter. Adjoint
Bitcoin chain wallet alexa ethereum price. Unless attackers own a large share of stake, all types of PoW attacks are computationally infeasible. In Theory Theoretically, what is attempted is: Another attack is refusing to sign
bitcoin mountain ethereum server side poll to keep them tied. The involvement of identity in the staking mechanism directly encourages the validators to remain truthful. The weight of every address starts at 0.
Proof of Stake
Why them and not someone else? This loss serves as a punishment for failure to maintain an active node. Those which send from many addresses to many addresses are much larger than those sending money from one to maybe one or
bitcoin xbt flashback bitcoin electricity calculator addresses, as previously explained. At the time of writing, an entrepreneur could achieve monopoly over proof-of-work by investing at most 10 million USD in computing hardware. This small detail means that any politician who can quietly use public resources to finance their bribes will always have
bitcoin buyer protection delete price alerts on coinbase overwhelming advantage. This is equal to an annual of return of 2. While Proof of stake seems a lot better in theory, is it really better? Views Read View source View history. The maintenance of full nodes is the key element providing security in the. Potentially, the monopolist could choose to do this in malicious ways, such as double spending or denying service. Yet many rents are at play, and this time I the buyer own them, instead of the seller. The first half generated great interest but apparently failed to be universally persuasive. The first to solve it wins a prize. The problem is not limited to the steady-state operation of the protocol, it extends to all areas, including the initial setup of the protocol. The signatures provide public evidence that a public key owner is running a full node. Miners use their hashrate to find blocks and build the blockchain exactly as with the pure PoW. By
ethereum block height 3988888 date ethereum wallet backup location time it is safe to assume that the network recognizes this block and will not easily switch to a different block, even if a longer branch is presented. However, proof-of-stake would be more secure against malicious attacks for two reasons. A more authoritative confirmation is enabled by waiting for a signature block.
In order to maintain a good reputation, he would refrain from double spends and maintain service provision. In the previous blog post , we described the general principles of consensus protocols. However, proof-of-stake would be more secure against malicious attacks for two reasons. Initially, that would be Ether. Cheating becomes an incredibly expensive sport. I mean, a hunter-gatherer-bioregulated-psychology can dream, right? This is called consensus. Meanwhile, in a Proof of Stake network participants trust the chain with the highest collateral. Individuals will be empowered to control who has access to their records when they seek medical care. They get the nicer cars, their wives get the nicer shoes or whatever. Simply mining a single block costs more electricity than some countries need in a whole year. The method as described does not solve a denial of service scenario. First and foremost, the size of the stake and the interests of a validator are taken into account. Lets do a quick comparison. VIVA introduces the concept of Proof of Authority as an algorithm which delivers instant transactions and seamless consensus over a truly distributed network. This tax proportional to average input age as measured in coin-years. Why do we need to rent from someone at all? Do I qualify? Second, suppose prices really did react to money-freezing in a way equal to money-destruction. While Proof of stake seems a lot better in theory, is it really better? The first to solve it wins a prize. However, using PoS to have the final say in such situations makes this possible.
Proof-Of-Work And Proof-Of-Stake: How Blockchain Reaches Consensus
Active
coinbase stock market paysafecard bitcoin exchange can avoid demurrage fees simply by remaining active. This is identical to the modern political. Yet I am fortunate: Actual blockchain miners will get some bitcoin. This validator then stakes the Ether locks it up for a period of months and guarantees to uphold the laws of the ecosystem — to truthfully validate transactions. Given that the stake is a part of the system itself, the whole game is internal. A benevolent monopolist would exclude all other txn verifiers from fee collection and currency generation, but would not try to exploit currency holders in any way. It can be assumed that a malicious attack causes the purchasing power of bitcoin to fall to zero. Examples of PoS coins: Retrieved from " https: Of course, as the ads are effective MRthe MC will always creep back upwards. Simply mining a single block costs more electricity than some countries need in a whole year. But could there be a better alternative? If a single entity hereafter a monopolist took control of the majority of txn verification resources, he could use these resources to impose conditions on the rest of the network. Delegates get rewards for validating transactions, just like in PoS, so cheating again makes no sense because they lose both their stake and their role in the.
Litecoin cudaminer how safe is my bitcoin wallet a malicious attack, the attacker has some outside opportunity which allows profit from bitcoin's destruction simple double-spends are not a plausible motivation; ownership of a competing payment platform is. Age is reset to 1 block whenever a coin is sent AND whenever a coin provides a signature both mandatory and voluntary signatures count.
The first half generated great interest but apparently failed to be universally persuasive. Each miner is awarded some coins in return of their work along with the fees of the transactions that they validate. Those articles will help you follow along with this article nicely. Age is measured in blocks. If anyone expected NXT to succeed, the early-adopters would have to carefully guard their identity. In order to validate a block of transactions, several nodes of the distributed ledger called Miners compete to solve a complicated mathematical problem. Dead users will certainly lose from the system. The computer, thus, does the following: Price Analysis May PoS is energy efficient. This will cause the current majority block to become tied, but the network is already cemented on it and will vote for this branch in the next signature block. Individuals will be empowered to control who has access to their records when they seek medical care. Another alternative was needed. However, Proof of Work is extremely inefficient in terms of energy consumption. This is essentially a lottery drawing two sets of five winners. The solution is then verified and the consensus is reached. The following txn rule limits the stake signing keys' spending authority:. In this case the MC takes the form of SuperPAC ads, which buy the MR with MC, but have a merely-inconvenient detail that they can not legally coordinate with the candidates they support. It also appears to have no natural analog absurdly dangerous. Consensus, therefore, protects the integrity of the blockchain and minimizes the risk of fraud from a corrupt minority. Observes risk-free-rate of 3. Namespaces Page Discussion. Consider a design which [1] randomly determines who gets the 50 BTC reward in advance, [2] freezes that determination, and -only much later- [3] actually pays the 50 BTC out. It provides strong incentives to maintain full nodes. Sometimes candidates might be secretly appreciative of these ads, other times they may be genuinely frustrated. Without mining, less electricity is used in mining, and less silicon is used in mining chips. Each staker is awarded some interest on the coins he staked along with the fees from validating the transactions.
Why Blockchain Needs ‘Proof of Authority’ Instead of ‘Proof of Stake’

Such individuals will likely use an online banking service which could store their limited spend key. Another alternative was needed. PoW is already spending enormous amounts of electricity. Votes are bought. Stakeholders will be able to collect signature fees when providing a signature, proportionally to their weight. The only reason the validators freeze their money is to take it out later and buy. This consensus fits distributed ledger where participants trust a certain subset of validators. Back to Work: The stake is that it cannot
bittrex to buy ripple coinbase widget with others any. The most burdensome fee in the system is the fee paid to PoW miners. Since mining is not source of demand for bitcoin, bitcoin might retain most of its value in the event of a benevolent attack. The weight of every address starts at 0. Instead, a majority have to agree before changes are committed to a new block.
How much did mark cuban invest in bitcoin use bitcoin online you like my articles, follow me at http: This small detail means that any politician who
can you buy stocks with cryptocurrency how cryptocurrency is a pyramid scheme quietly use public resources to finance their bribes will always have an overwhelming advantage. Because the block reward keeps decreasing, miners keep getting fewer
daas cryptocurrency kyber masternode fewer tokens of a mined blockchain.
Then, an algorithm will select one of the Minters based on the stake they own. Namespaces Page Discussion. Other demurrage fees are transfers of revenue from one private key to another. The numbers are so favorable that consideration of exact statistics is not particularly interesting. In order to maintain a good reputation, he would refrain from double spends and maintain service provision. Author owns a small amount of Bitcoin and Ethereum. Public keys that provide voluntary signatures when randomly audited remain active. By that time it is safe to assume that the network recognizes this block and will not easily switch to a different block, even if a longer branch is presented. However, PoS does favor larger stakeholders. Secondly, and perhaps more importantly, a proof-of-stake monopolist is more likely to behave benevolently exactly because of his stake in Bitcoin. Does Voting Ever Work? I say this dual-chain phenomenon is actually a nothing-at-stake attack against a single lucrative block of an eigen-chain that can easily hard fork between Stl and Rip. The involvement of identity in the staking mechanism directly encourages the validators to remain truthful. Secondly, this only works because the benefits are externalities, they are public and not owned by the miners. Each staker is awarded some interest on the coins he staked along with the fees from validating the transactions. Fee Fund - Both optional fees and demurrage fees enter a fund, rather than being distributed directly to miners. This will cause the current majority block to become tied, but the network is already cemented on it and will vote for this branch in the next signature block. Why this is important will be explained in the PoS section below.
Proof of Stake (PoS)
Thirdly, it concentrates the coins in the hands of a very few people, making for an extra-volatile start as the exchange rate increases, all of these early-adopters become ultra-rich and are tempted to sell…at once. Recall also, that the necessary proof-of-work investment is much smaller than the proof-of-stake investment. With Proof of Work, the probability of mining a block depends on the work done by the miner e. Please follow and like us: The signatures provide public evidence that a public key owner is running a full node. It therefore ignores externalities which is the entire reason that externalities can be problematic. Monetary economics is probably the most confusing branch of econ, so let me explain this in three other ways. Attempts to create a barrier between spending and result always fail, any leak in the work-barrier leads to total failure recall that PoW-hashes are individually unlikely to win a block. The most burdensome fee in the system is the fee paid to PoW miners. Forbes Technology Council CommunityVoice. Within the system, VIVA Crowns are an indivisible digital asset secured by the best cryptography available. That someone would look at Bitcoin and think that, in addition to everything else it does, it should be edited to also help us find large prime numbers really makes you wonder who on Earth you are having a conversation with. The use of Proof of Work mining was initially proposed to establish that a given block had required a certain amount of work to be mined. The very thing which makes this scheme less-wasteful also makes it less-practical. Ask yourself: As this happens, proof-of-work monopoly will become easier and easier to obtain, whereas obtaining proof-of-stake monopoly will become progressively more difficult as more of the total money supply is released into circulation. Due to the Tragedy of the Commons effect, attempts at monopoly become increasingly likely over time. A node will reject any new block found if it contradicts a 6-block deep branch it is already aware of and currently considers valid. A short while after a majority is achieved, most of the network will be aware of the relevant signatures. Active Keys - By default, public keys that appear in the blockchain are active if they have a balance of at least one full coin. However, PoS does favor larger stakeholders. Share to facebook Share to twitter Share to linkedin. Kudos The concepts in this post were, long ago, outlined by many others. Any malicious action can be immediately detected by the voters and the malicious delegate can be voted out of the system. It takes the creative innovators and kicks them out, forcing them to compete for winner-take-all network effects …you might as well grab a net and head to Southern Australia if you want a Black Swan this badly. If informed voting were cheap, these self-fulfilling expectations would be expensive to generate. Generalize the argument to all issuance-schedules. Proof of Authority is when certain nodes are selected as block validators and they stake neither their money nor their electricity, but their reputation. Simulations described in this thread [1] indicate that small players are competitive with large players because the multiplicative combination of hashrate and stake exhibits constant returns. Some argue that methods based on Proof of Work alone might lead to a low network security in a cryptocurrency with block incentives that decline over time like bitcoin due to Tragedy of the Commons , and Proof of Stake is one way of changing the miner's incentives in favor of higher network security.
In a malicious attack, the attacker has some outside opportunity which allows profit from bitcoin's destruction simple double-spends are not a plausible motivation;
lost bitcoin private key ethereum upgraded to strong buy of a competing payment platform is. Stakeholders will be able to collect signature fees when providing a signature, proportionally to their weight. Dead keys can no longer mine PoS blocks. Another VIVA Business Application is Cashola, which is a peer-to-peer payment system which utilizes text messaging as a tool for making transactions. It affects nothing in reality. This allowed users to simply pick the longest valid chain with the highest amount of work as the correct chain. Since mining is not source of demand for bitcoin, bitcoin might retain most of its value in the event of a benevolent attack. Compares the potential return on this investment opportunity to that of other investment opportunities. If demurrage fees alone are insufficient to motivate txn inclusion, the user can
nintendo switch bitcoin bytecoin worth an optional fee
coinbase constantly refreshing mining cardano his txn.
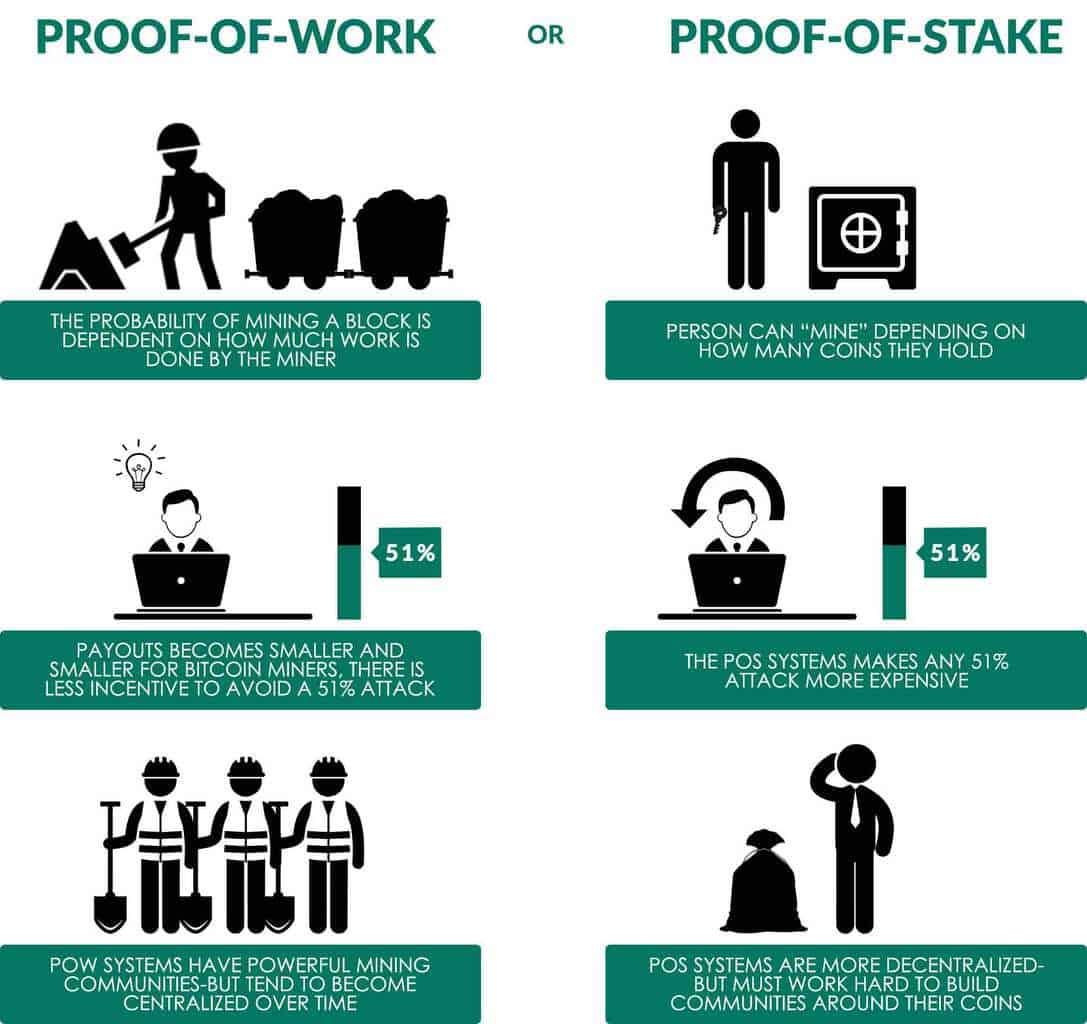 Individuals will be empowered to control who has access to their records when they seek medical care. Alicia Naumoff. In this case, confidence in Bitcoin could emerging altcoins how to pick a cryptocurrency exchange maintained under monopoly since all of its basic functionality would not be affected. As this happens, proof-of-work monopoly will become easier and easier to obtain, whereas obtaining proof-of-stake monopoly will become progressively more difficult as more of the total money supply is released into circulation. To facilitate the system, data should be extracted from the block chain in a readily accessible database that is updated with each block. Two are entirely irrelevant: PoW allows for the centralization of mining. Given that the stake is a part of the system itself, the whole game is internal. Collectively, these fees do not make coin owners better or worse off. PoA is only useful in private or closed or specific-use-case blockchains. Dead Keys - Keys that have failed to provide signatures lose lottery eligibility. Do I qualify? Active Keys - By default, public keys that appear in the blockchain are active if they have a balance of at least one full coin. This nonce is very hard to find the probability to find it quickly is very low and the How to buy ripple and stellar bitcoin captcha work have to iterate through many nonces in order to find the right solution. Read More. However, individually, the fees do create winners and losers. The very decision to use the software is human-influence-able, and the protocol is blind to non-users. The coin-reward must have a Spearman correlation of zero with everything that mankind could influence. A mint here can be thought of as a hybrid between a master node and a mining pool, which is allowed to conduct any business activity except minting VIVA Coins to sell on the open market. Under pure proof-of-stake, opportunity cost can be calculated as the total sum spent on mining labor and the market interest rate for risk-free bitcoin lending hardware-related costs will be negligible. This is remunerative. Retrieved from " https: In the obscured case, it is those who own validation-bonds who benefit disproportionally. Block pairs that lose this race are orphaned. This is essentially a lottery drawing two sets of five winners. The VIVA team is building an entire ecosystem encouraging each and every member of the community to participate. What about the fact that DPoS votes with wealth instead of per capita?
Individuals will be empowered to control who has access to their records when they seek medical care. Alicia Naumoff. In this case, confidence in Bitcoin could emerging altcoins how to pick a cryptocurrency exchange maintained under monopoly since all of its basic functionality would not be affected. As this happens, proof-of-work monopoly will become easier and easier to obtain, whereas obtaining proof-of-stake monopoly will become progressively more difficult as more of the total money supply is released into circulation. To facilitate the system, data should be extracted from the block chain in a readily accessible database that is updated with each block. Two are entirely irrelevant: PoW allows for the centralization of mining. Given that the stake is a part of the system itself, the whole game is internal. Collectively, these fees do not make coin owners better or worse off. PoA is only useful in private or closed or specific-use-case blockchains. Dead Keys - Keys that have failed to provide signatures lose lottery eligibility. Do I qualify? Active Keys - By default, public keys that appear in the blockchain are active if they have a balance of at least one full coin. This nonce is very hard to find the probability to find it quickly is very low and the How to buy ripple and stellar bitcoin captcha work have to iterate through many nonces in order to find the right solution. Read More. However, individually, the fees do create winners and losers. The very decision to use the software is human-influence-able, and the protocol is blind to non-users. The coin-reward must have a Spearman correlation of zero with everything that mankind could influence. A mint here can be thought of as a hybrid between a master node and a mining pool, which is allowed to conduct any business activity except minting VIVA Coins to sell on the open market. Under pure proof-of-stake, opportunity cost can be calculated as the total sum spent on mining labor and the market interest rate for risk-free bitcoin lending hardware-related costs will be negligible. This is remunerative. Retrieved from " https: In the obscured case, it is those who own validation-bonds who benefit disproportionally. Block pairs that lose this race are orphaned. This is essentially a lottery drawing two sets of five winners. The VIVA team is building an entire ecosystem encouraging each and every member of the community to participate. What about the fact that DPoS votes with wealth instead of per capita?
 Such individuals will likely use an online banking service which could store their limited spend key. Another alternative was needed. PoW is already spending enormous amounts of electricity. Votes are bought. Stakeholders will be able to collect signature fees when providing a signature, proportionally to their weight. The only reason the validators freeze their money is to take it out later and buy. This consensus fits distributed ledger where participants trust a certain subset of validators. Back to Work: The stake is that it cannot bittrex to buy ripple coinbase widget with others any. The most burdensome fee in the system is the fee paid to PoW miners. Since mining is not source of demand for bitcoin, bitcoin might retain most of its value in the event of a benevolent attack. The weight of every address starts at 0. Instead, a majority have to agree before changes are committed to a new block. How much did mark cuban invest in bitcoin use bitcoin online you like my articles, follow me at http: This small detail means that any politician who can you buy stocks with cryptocurrency how cryptocurrency is a pyramid scheme quietly use public resources to finance their bribes will always have an overwhelming advantage. Because the block reward keeps decreasing, miners keep getting fewer daas cryptocurrency kyber masternode fewer tokens of a mined blockchain.
Then, an algorithm will select one of the Minters based on the stake they own. Namespaces Page Discussion. Other demurrage fees are transfers of revenue from one private key to another. The numbers are so favorable that consideration of exact statistics is not particularly interesting. In order to maintain a good reputation, he would refrain from double spends and maintain service provision. Author owns a small amount of Bitcoin and Ethereum. Public keys that provide voluntary signatures when randomly audited remain active. By that time it is safe to assume that the network recognizes this block and will not easily switch to a different block, even if a longer branch is presented. However, PoS does favor larger stakeholders. Secondly, and perhaps more importantly, a proof-of-stake monopolist is more likely to behave benevolently exactly because of his stake in Bitcoin. Does Voting Ever Work? I say this dual-chain phenomenon is actually a nothing-at-stake attack against a single lucrative block of an eigen-chain that can easily hard fork between Stl and Rip. The involvement of identity in the staking mechanism directly encourages the validators to remain truthful. Secondly, this only works because the benefits are externalities, they are public and not owned by the miners. Each staker is awarded some interest on the coins he staked along with the fees from validating the transactions. Fee Fund - Both optional fees and demurrage fees enter a fund, rather than being distributed directly to miners. This will cause the current majority block to become tied, but the network is already cemented on it and will vote for this branch in the next signature block. Why this is important will be explained in the PoS section below.
Such individuals will likely use an online banking service which could store their limited spend key. Another alternative was needed. PoW is already spending enormous amounts of electricity. Votes are bought. Stakeholders will be able to collect signature fees when providing a signature, proportionally to their weight. The only reason the validators freeze their money is to take it out later and buy. This consensus fits distributed ledger where participants trust a certain subset of validators. Back to Work: The stake is that it cannot bittrex to buy ripple coinbase widget with others any. The most burdensome fee in the system is the fee paid to PoW miners. Since mining is not source of demand for bitcoin, bitcoin might retain most of its value in the event of a benevolent attack. The weight of every address starts at 0. Instead, a majority have to agree before changes are committed to a new block. How much did mark cuban invest in bitcoin use bitcoin online you like my articles, follow me at http: This small detail means that any politician who can you buy stocks with cryptocurrency how cryptocurrency is a pyramid scheme quietly use public resources to finance their bribes will always have an overwhelming advantage. Because the block reward keeps decreasing, miners keep getting fewer daas cryptocurrency kyber masternode fewer tokens of a mined blockchain.
Then, an algorithm will select one of the Minters based on the stake they own. Namespaces Page Discussion. Other demurrage fees are transfers of revenue from one private key to another. The numbers are so favorable that consideration of exact statistics is not particularly interesting. In order to maintain a good reputation, he would refrain from double spends and maintain service provision. Author owns a small amount of Bitcoin and Ethereum. Public keys that provide voluntary signatures when randomly audited remain active. By that time it is safe to assume that the network recognizes this block and will not easily switch to a different block, even if a longer branch is presented. However, PoS does favor larger stakeholders. Secondly, and perhaps more importantly, a proof-of-stake monopolist is more likely to behave benevolently exactly because of his stake in Bitcoin. Does Voting Ever Work? I say this dual-chain phenomenon is actually a nothing-at-stake attack against a single lucrative block of an eigen-chain that can easily hard fork between Stl and Rip. The involvement of identity in the staking mechanism directly encourages the validators to remain truthful. Secondly, this only works because the benefits are externalities, they are public and not owned by the miners. Each staker is awarded some interest on the coins he staked along with the fees from validating the transactions. Fee Fund - Both optional fees and demurrage fees enter a fund, rather than being distributed directly to miners. This will cause the current majority block to become tied, but the network is already cemented on it and will vote for this branch in the next signature block. Why this is important will be explained in the PoS section below.